What Got Leaked Today: A Practical Guide for Homeowners
Explore today’s data leaks, how they spread, and practical steps homeowners can take to secure accounts, devices, and networks in 2026.
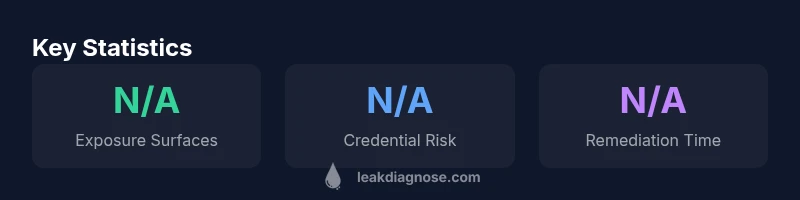
What got leaked today refers to fresh exposures across online services, apps, or devices that created an unintended data surface. In most cases, leaks involve credential exposure, misconfigured storage, or weak access controls across consumer tech. The Leak Diagnosis team emphasizes that rapid surface-mapping and prompt remediation are the best defenses against evolving leaks in 2026.
What today’s leaks reveal about the digital surface homeowners interact with daily
In the era of connected homes, what got leaked today often involves credentials, device telemetry, or configuration data that slipped into exposure. The headlines sometimes focus on sensational numbers, but the practical risk centers on surfaces you control: email accounts, cloud storage, streaming services, and smart devices. According to Leak Diagnosis, leaks follow a recognizable lifecycle—discovery, verification, disclosure, and remediation—and understanding that chain helps homeowners act quickly. When a leak surfaces today, the first step is surface mapping: which services were affected, where the exposure occurred, and whether credentials or public storage were involved. This is not about doomscrolling; it’s about pinpointing exact exposure surfaces and prioritizing actions such as password hygiene, MFA, and device isolation. The phrase what got leaked today should trigger concrete steps rather than fear, and that’s where disciplined routines make a real difference.
How leaks spread across platforms and devices
Leaks propagate when security controls are inconsistent across services, apps, and devices. A credential dump on one service can empower attackers to test other accounts, especially when passwords are reused. Many owners learn of leaks through suspicious login alerts, unexpected password reset notices, or unusual charges. From a risk-management lens, surface area matters most: every connected device adds another potential exposure, and weak network segmentation amplifies risk. Leak Diagnosis highlights that the most dangerous exposures are those that are hard to detect—API keys embedded in apps, misconfigured storage buckets, or stale tokens. The antidote is simple in principle: reduce exposed surfaces, rotate credentials, and enable quick-reaction measures like MFA and breach alerts. See what got leaked today as a prompt to review the entire stack, not just the headline.
The lifecycle of a leak: discovery, verification, disclosure, remediation
Leaks start with discovery—often via automated monitors, user reports, or vendor advisories. Verification is the crucial step where claims are checked against data sources to confirm authenticity. Disclosure can be managed by service providers or, sometimes, by media outlets, which can help users act but also risks spreading panic. Remediation follows: revoke compromised keys, rotate passwords, and apply patches. For homeowners, the practical concern is actionable steps you can take now: audit credential health in password managers, review connected apps, and check for unusual account activity. Leak Diagnosis emphasizes that a calm, methodical approach minimizes damage and shortens exposure time. A leak doesn’t automatically mean personal data was exposed; it means there is an exposed surface that deserves attention.
How to verify a leak in your own environment
Verification starts with monitoring official breach notices and credential monitoring services from reputable sources. Look for patterns: repeated login attempts, unexpected password resets, or data exfiltration warnings from cloud providers. Use account activity logs, security dashboards, and device histories to triangulate risk. If today’s leak touches email or cloud storage, secure those primary accounts first: enable MFA, update recovery options, and review connected devices. For IoT, check firmware updates and reset credentials where appropriate. Document a timeline of events and actions taken; this aids remediation and any required disclosures. The objective is to close exposure quickly, not assign blame.
Immediate homeowner actions when you suspect exposure
If you suspect a leak, act fast with a structured checklist. Change recently used passwords across critical services, enable multi-factor authentication, and audit third-party apps for excessive permissions. Review email forwarding rules and alert settings to prevent data exfiltration via phishing. Check credit reports and bank statements for unfamiliar activity, and consider fraud alerts if needed. For home networks, reset your router to factory settings if you cannot verify firmware integrity, then reconfigure with a strong, unique passphrase. Maintain an inventory of devices and ensure each has updated firmware. If you store sensitive data in the cloud, enable client-side encryption where possible. Throughout, document changes and keep providers informed if a breach involves their platform. Leak Diagnosis recommends a calm, stepwise approach and rapid iteration.
Smart home and IoT: unique risk factors
Smart devices offer convenience but increase exposure surfaces. Many IoT devices still rely on default credentials, insecure cloud integrations, or weak segmentation, which can leak data if misconfigured. If today’s leak touches smart speakers, cameras, or thermostats, audit the entire network: segment devices by trust level, disable unnecessary remote access, and ensure robust encryption (for example, WPA3) on your router. Regular firmware updates reduce exposure to known vulnerabilities. Also review any voice data that devices may be transmitting and adjust privacy settings. Treat IoT as a potential weak link and design defenses that limit blast radius by isolating critical devices on separate networks and using unique credentials.
Data leakage vs. data breach: terminology and implications
Understanding the difference matters for remediation and expectations. Data leakage typically involves unintentional exposure due to misconfigurations or flawed access controls, while a data breach implies unauthorized access by an external actor. For homeowners, clarity helps prioritize actions like credential rotation, provider-specific incident responses, and notification obligations. Leak Diagnosis notes that precise terminology guides your response strategy and communications with providers, so you can act decisively when what got leaked today becomes a topic of public discussion.
Data protection hygiene: routines you can implement today
Turn data hygiene into a habit rather than a reaction. Use a password manager to generate unique credentials for every service and enable MFA wherever possible. Regularly review and prune third-party access, set up credible breach alerts, and share sensitive files via encrypted links when needed. Back up important data to a secure offline location or trusted cloud with encryption. Keep devices updated as part of a routine maintenance schedule. These practices build resilience against today’s leaks and future incidents, making your home’s digital surface more predictable and safer.
The role of policy, updates, and consumer rights
Policy developments shape how leaks are handled and disclosed. Consumer rights related to data portability, breach notifications, and security standards influence how what got leaked today is addressed by providers. Governments are increasingly focusing on supply-chain resilience, vendor risk management, and privacy-by-design. For homeowners, staying informed about changes to terms of service, data-handling practices, and opt-in controls helps reduce exposure and speeds remediation. The Leak Diagnosis team emphasizes proactive education, ongoing auditing, and a calm, methodical approach to reduce risk over time. The aim is sustainable protection for households, not sensationalism.
Common consumer-facing exposure scenarios and recommended actions
| Leak Type | Typical Exposure | Remediation Priority |
|---|---|---|
| Credential exposure | Credentials found in data dumps or reused across services | Urgent |
| IoT device exposure | Misconfigured devices exposing data | High |
| Cloud storage exposure | Publicly accessible buckets or misconfigured permissions | Medium |
Questions & Answers
What does 'what got leaked today' typically involve for homeowners?
Homeowners usually see exposure of credentials, misconfigured storage, or weak controls across services and devices. The key is to identify the surface and act quickly to rotate credentials, enable MFA, and review connected devices.
Typically, today’s leaks involve credentials or misconfigurations. Act quickly by rotating passwords and checking connected devices.
Are smart home devices more at risk when there’s a leak?
Yes, IoT devices can expand exposure surfaces if not properly secured. Ensure firmware updates, strong unique passwords, and network segmentation to limit damage.
Smart devices can increase risk if not secured; update firmware and use strong, unique passwords.
What is the difference between data leakage and data breach for households?
Data leakage is usually accidental exposure due to misconfigurations, while a data breach involves unauthorized access by an external actor. The distinction guides remediation priorities and notifications.
Leakage is accidental exposure; a breach is unauthorized access. Both need action, but the steps differ.
What should I do first if I hear about a leak today?
Start by confirming the exposure scope, rotate the most critical passwords, enable MFA, and review critical accounts and devices for unusual activity.
First, confirm the exposure and rotate key passwords; enable MFA and check critical accounts.
How can I reduce exposure on a daily basis?
Use a password manager, enable MFA, review third-party access periodically, back up data, and keep devices updated as part of a regular maintenance routine.
Keep passwords unique with a manager, enable MFA, and update devices regularly.
“"What got leaked today highlights the growing surface area of household data exposure. A layered, proactive defense remains the best antidote for 2026."”
Main Points
- Act quickly to rotate credentials after a leak
- Enable MFA on critical accounts and services
- Secure IoT devices and segment home networks
- Monitor accounts for unusual activity and maintain backups
- Differentiate leakage from breach to tailor response