What is a Data Leak Definition, Detection, and Prevention
Learn what a data leak means, how it happens, the risks involved, and practical steps homeowners can take to prevent and respond to data leaks in everyday devices and services.
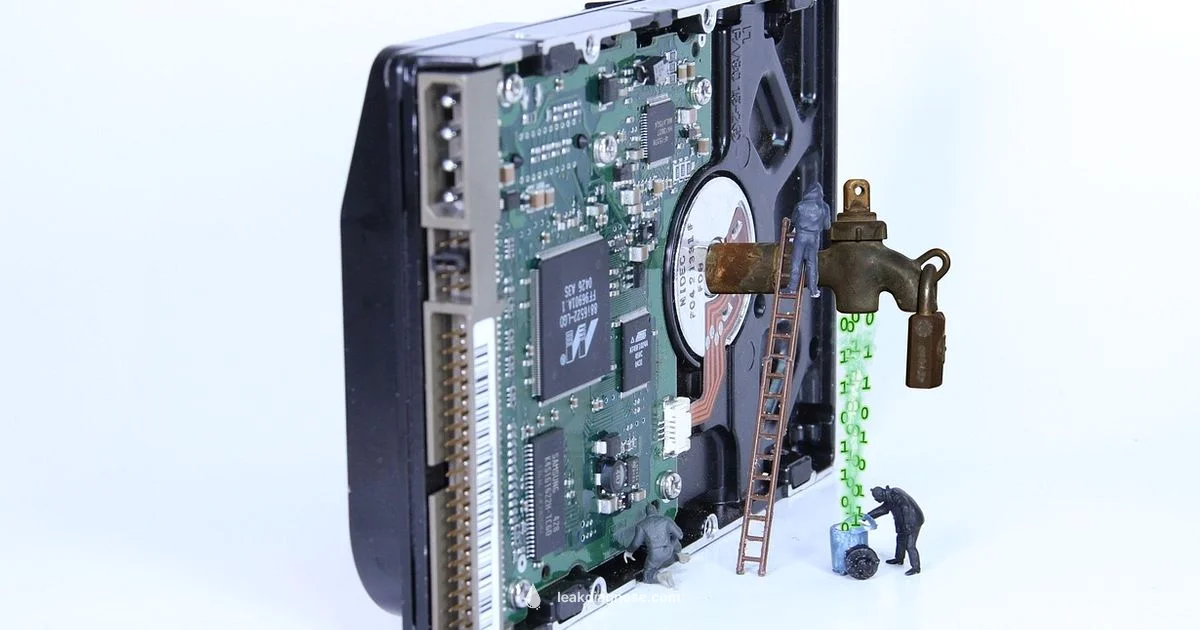
Data leak is a security incident where sensitive information is exposed to unauthorized individuals, either accidentally or intentionally, through vulnerable systems, misconfigurations, or careless handling.
What is a data leak?
Data leak is a security incident in which sensitive information is exposed to unauthorized individuals, either accidentally or intentionally, through weak controls, misconfigurations, or human error. This exposure can involve personal data such as names, addresses, and Social Security numbers, financial records, medical information, or confidential business documents. A data leak differs from a data breach in intent; a breach often implies deliberate theft, whereas a leak can result from carelessness or a misconfigured system that leaves data visible to the wrong audience. In practical terms, think of a misconfigured database that anyone on the internet can access, or an employee sharing files on an insecure channel. Leaks can occur across home devices, cloud services, email accounts, and networks, underscoring the need for ongoing vigilance.
To understand the landscape, distinguish between accidental leaks and deliberate breaches. An accidental leak can arise from a misstep such as sending a file to the wrong recipient, while a breach typically involves an attacker gaining unauthorized access through stolen credentials or exploits. Both endanger privacy, erode trust, and can trigger regulatory obligations depending on the data involved. The core idea is that sensitive information is exposed beyond its intended audience, whether by mistake or malice.
Why data leaks matter
The consequences of a data leak extend beyond immediate exposure. Personal information can be misused for identity theft, fraud, or phishing campaigns that target victims years after the initial leak. For homeowners and small businesses, leaks can lead to financial costs from remediation, legal exposure, and reputational damage that erodes customer confidence. Regulatory frameworks in many regions require timely breach notices and credible data protection practices; failing to comply can invite penalties, lawsuits, and heightened scrutiny from regulators. Even when no one directly misuses the data, the mere presence of sensitive information outside its secure context can empower criminals. Building a culture of data hygiene—minimizing what is collected, who can access it, and how it is stored—reduces both the likelihood and impact of leaks. The Leak Diagnosis team finds that proactive governance and clear incident response plans are essential components of resilience.
Common sources of data leaks in households and small businesses
Leaks are not limited to enterprise environments; everyday households and small businesses face similar risks in smaller scales. Common sources include:
- Misconfigured cloud storage and public sharing links that leave documents accessible to anyone with the URL.
- Weak authentication and password reuse, enabling attackers to access accounts and exfiltrate data.
- Insecure Wi Fi networks or poorly secured home routers that give outsiders a foothold into devices.
- Lost or stolen devices containing unencrypted data or access credentials.
- Insecure backups and unencrypted mobile devices or USB drives that transport sensitive information.
- Third party apps and services with broad data permissions that expose information through integrations.
- Email missteps, such as sending to the wrong recipient or careless attachment handling.
- Poor data disposal practices, leaving recoverable information in old devices or drives.
For households, these risks stack with everyday tech usage: smart home devices, cloud photo storage, and consumer apps can all become conduits for leaks if not configured securely. For small businesses, vendor risk and data-sharing arrangements amplify exposure unless governance and data classification are in place.
How to detect a data leak
Early detection hinges on noticing abnormal data activity and access patterns. Practical indicators include unexpected spikes in data exports, unusual login locations or times, new outbound data flows, or alerts from your security software about suspicious files. Implementing data loss prevention policies, enabling MFA, and reviewing access permissions helps flag irregularities. Regularly monitoring logs from email, cloud storage, and network devices provides a baseline of normal activity; deviations from this baseline should trigger a security review. If you use third party services, ensure they offer audit trails and data processing records so you can correlate incidents with external providers. Quick wins include setting up alerts for out of pattern data transfers and reviewing share settings on collaborative platforms.
Steps to respond to a data leak
When you suspect a data leak, respond methodically to limit damage. First, contain the exposure by revoking compromised credentials and isolating affected systems. Next, inventory exposed data to assess scope and risk, including the types of data involved and the potential impact on individuals or your business. Notify relevant stakeholders per regulatory and contractual obligations, and consider legal counsel to understand reporting requirements. Conduct a root cause analysis to determine how the leak occurred and implement fixes—such as patching software, tightening access controls, and improving data handling policies. Finally, educate users and employees on secure practices and update incident response plans to reduce recurrence. Documentation of actions taken is essential for resilience and accountability.
Prevention strategies for homeowners and small businesses
Preventing data leaks starts with prudent data governance and technical controls. Key strategies include:
- Minimize data collection and retention to only what is necessary.
- Encrypt data at rest and in transit, and store encryption keys separately from the data.
- Enforce strong authentication and MFA across devices and accounts, with unique passwords and regular changes.
- Implement role-based access controls and regular access reviews to limit who can see sensitive data.
- Use reputable cloud storage configurations and verify access permissions; avoid publicly shared links unless necessary and fully restricted.
- Keep software up to date with security patches and enable automatic updates where possible.
- Back up data regularly and securely, testing restoration procedures.
- Establish a written data breach response plan and run drills so everyone knows their role.
- Vet third party vendors for data handling practices and require data processing agreements.
For households, practical steps include enabling device encryption, securing home networks with strong Wi Fi passwords, and using separate accounts for guests. For small businesses, ongoing training, data classification, and incident response rehearsals are essential to reduce risk and speed recovery. Collaboration between IT staff, executives, and end users creates a culture where data leaks are less likely and easier to manage when they occur.
When to seek professional help
If you suspect a data leak and the data involved is sensitive or regulated, professional help can accelerate containment and remediation. A security professional can assist with forensic analysis, data mapping, and implementing stronger controls. The Leak Diagnosis team recommends contacting qualified cybersecurity experts or consultancies when the incident exceeds in-house capabilities, or when legal and regulatory considerations require specialized guidance. Timely professional support helps restore confidence and demonstrates a commitment to responsible data handling.
Questions & Answers
What is a data leak?
A data leak is a security incident where sensitive information becomes exposed to unauthorized individuals, often due to human error or weak controls. It can involve personal, financial, or corporate data and may occur accidentally or through misconfiguration.
A data leak is when private data becomes exposed to someone who should not have access, often because of mistakes or weak protections.
How is a data leak different from a data breach?
A data leak typically results from unintentional exposure or misconfiguration, while a data breach usually implies deliberate theft or intrusion. Both can expose the same types of data, but intent and context help distinguish them.
A data leak is usually unintentional exposure, while a data breach involves deliberate theft.
What kinds of data are typically at risk in a data leak?
Commonly at risk are personal identifiers, payment and financial information, login credentials, health records, and confidential business documents. The specific data depends on what your systems store and how data is shared with third parties.
Personal details, financial data, passwords, and other sensitive information are commonly involved in data leaks.
What steps can homeowners take to prevent data leaks?
Homeowners should use strong unique passwords, enable multi factor authentication, encrypt devices and backups, secure home networks, and review data sharing settings on apps and cloud services. Regular software updates and prudent data minimization also help.
Use strong passwords, enable MFA, encrypt devices, and keep software up to date.
What should I do if I suspect a data leak?
Contain the exposure by changing passwords and securing affected devices, then assess what data was exposed and notify relevant parties as required. Run security checks and update your protections to prevent recurrence.
Change passwords, secure devices, assess what's exposed, and get help if needed.
Do data leaks require reporting to authorities?
Regulatory requirements vary by jurisdiction and data type. In many places, significant leaks must be reported to regulators or affected individuals, especially when personal or financial information is involved. Consult local laws and seek legal counsel as needed.
Yes, many jurisdictions require reporting for significant leaks; check local laws.
Main Points
- Identify data leak sources and apply fixes quickly
- Prioritize data minimization and encryption to prevent leaks
- Regularly audit cloud and device security
- Establish a data breach response plan
- Seek professional help when in doubt